Jan 11, 2024NewsroomVulnerability / Patch Management Cisco has released software updates to address a critical security flaw impacting Unity Connection that could permit an adversary to execute arbitrary commands on the underlying system. Tracked as CVE-2024-20272 (CVSS score: 7.3), the vulnerability is an arbitrary file upload bug residing in the web-based management interface and is the result … [Read more...]
NoaBot: Latest Mirai-Based Botnet Targeting SSH Servers for Crypto Mining
Jan 10, 2024NewsroomServer Security / Cryptocurrency A new Mirai-based botnet called NoaBot is being used by threat actors as part of a crypto mining campaign since the beginning of 2023. "The capabilities of the new botnet, NoaBot, include a wormable self-spreader and an SSH key backdoor to download and execute additional binaries or spread itself to new victims," Akamai security researcher … [Read more...]
Getting off the Attack Surface Hamster Wheel: Identity Can Help
IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and how to manage it. The process is simple: begin by thoroughly assessing the attack surface, encompassing the entire IT environment. Identify all potential entry and exit points where unauthorized access could occur. Strengthen these vulnerable points using available … [Read more...]
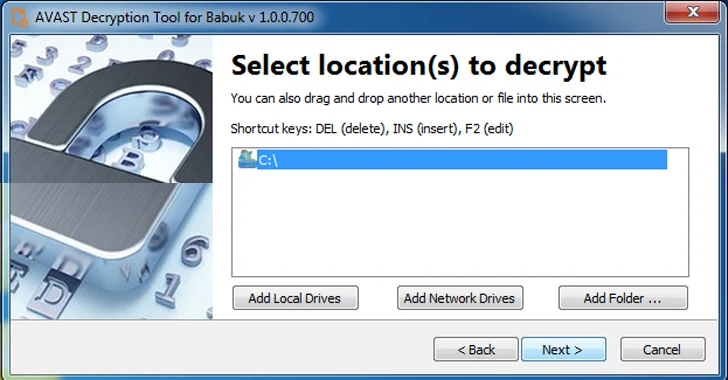
Free Decryptor Released for Black Basta and Babuk's Tortilla Ransomware Victims
Jan 10, 2024NewsroomRansomware / Data Security A decryptor for the Tortilla variant of the Babuk ransomware has been released by Cisco Talos, allowing victims targeted by the malware to regain access to their files. The cybersecurity firm said the threat intelligence it shared with Dutch law enforcement authorities made it possible to arrest the threat actor behind the operations. The encryption … [Read more...]
FTC Bans Outlogic (X-Mode) From Selling Sensitive Location Data
Jan 10, 2024NewsroomPrivacy / Regulatory Compliance The U.S. Federal Trade Commission (FTC) on Tuesday prohibited data broker Outlogic, which was previously known as X-Mode Social, from sharing or selling any sensitive location data with third-parties. The ban is part of a settlement over allegations that the company "sold precise location data that could be used to track people's visits to … [Read more...]
Microsoft's January 2024 Windows Update Patches 48 New Vulnerabilities
Jan 10, 2024NewsroomVulnerability / Windows Security Microsoft has addressed a total of 48 security flaws spanning its software as part of its Patch Tuesday updates for January 2024. Of the 48 bugs, two are rated Critical and 46 are rated Important in severity. There is no evidence that any of the issues are publicly known or under active attack at the time of release, making it the second … [Read more...]
CISA Flags 6 Vulnerabilities – Apple, Apache, Adobe , D-Link, Joomla Under Attack
Jan 10, 2024NewsroomPatch Management / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. This includes CVE-2023-27524 (CVSS score: 8.9), a high-severity vulnerability impacting the Apache Superset open-source data visualization software … [Read more...]
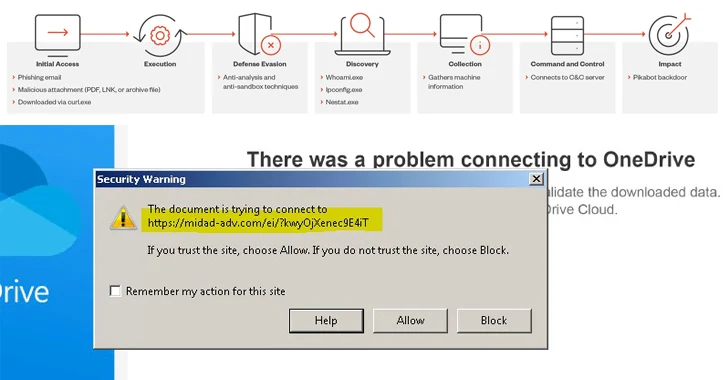
Alert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware
Jan 09, 2024NewsroomMalware / Cyber Threat A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware as part of spam campaigns in 2023. "PikaBot's operators ran phishing campaigns, targeting victims via its two components — a loader and a core module — which enabled unauthorized remote access and allowed the execution of arbitrary commands through an … [Read more...]
Turkish Hackers Exploiting Poorly Secured MS SQL Servers Across the Globe
Jan 09, 2024NewsroomData Security / Cyber Attack Poorly secured Microsoft SQL (MS SQL) servers are being targeted in the U.S., European Union, and Latin American (LATAM) regions as part of an ongoing financially motivated campaign to gain initial access. "The analyzed threat campaign appears to end in one of two ways, either the selling of 'access' to the compromised host, or the ultimate … [Read more...]
Why Public Links Expose Your SaaS Attack Surface
Jan 09, 2024The Hacker NewsSaaS Security / Data Security Collaboration is a powerful selling point for SaaS applications. Microsoft, Github, Miro, and others promote the collaborative nature of their software applications that allows users to do more. Links to files, repositories, and boards can be shared with anyone, anywhere. This encourages teamwork that helps create stronger campaigns and … [Read more...]
Alert: New Vulnerabilities Discovered in QNAP and Kyocera Device Manager
Jan 09, 2024NewsroomNetwork Security / Data Protection A security flaw has been disclosed in Kyocera's Device Manager product that could be exploited by bad actors to carry out malicious activities on affected systems. "This vulnerability allows attackers to coerce authentication attempts to their own resources, such as a malicious SMB share, to capture or relay Active Directory hashed … [Read more...]
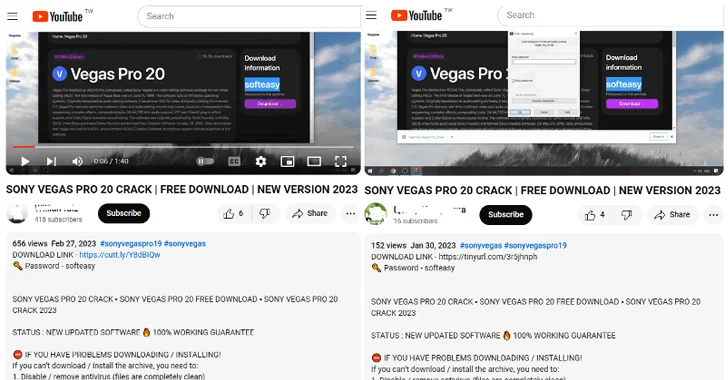
Beware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer
Jan 09, 2024NewsroomMalware / Cyber Threat Threat actors are resorting to YouTube videos featuring content related to cracked software in order to entice users into downloading an information stealer malware called Lumma. "These YouTube videos typically feature content related to cracked applications, presenting users with similar installation guides and incorporating malicious URLs often … [Read more...]
Syrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Jan 08, 2024NewsroomMalware / Cybercrime Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that's equipped to bypass security software and stealthily launch hidden applications. "The developers operate on multiple hacker forums and social media platforms, showcasing an active and sophisticated presence," cybersecurity firm … [Read more...]
Unifying Security Tech Beyond the Stack: Integrating SecOps with Managed Risk and Strategy
Cybersecurity is an infinite journey in a digital landscape that never ceases to change. According to Ponemon Institute1, "only 59% of organizations say their cybersecurity strategy has changed over the past two years." This stagnation in strategy adaptation can be traced back to several key issues. Talent Retention Challenges: The cybersecurity field is rapidly advancing, requiring a skilled and … [Read more...]
Webinar – Leverage Zero Trust Security to Minimize Your Attack Surface
Jan 08, 2024NewsroomCyber Security / Zero Trust Digital expansion inevitably increases the external attack surface, making you susceptible to cyberthreats. Threat actors increasingly exploit the vulnerabilities stemming from software and infrastructure exposed to the internet; this ironically includes security tools, particularly firewalls and VPNs, which give attackers direct network access to … [Read more...]
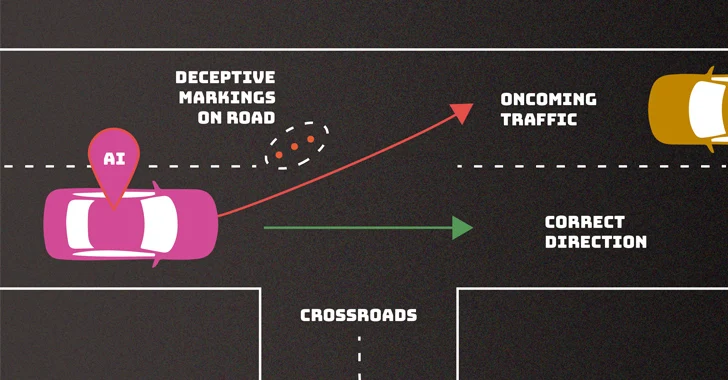
NIST Warns of Security and Privacy Risks from Rapid AI System Deployment
Jan 08, 2024NewsroomArtificial Intelligence / Cyber Security The U.S. National Institute of Standards and Technology (NIST) is calling attention to the privacy and security challenges that arise as a result of increased deployment of artificial intelligence (AI) systems in recent years. "These security and privacy challenges include the potential for adversarial manipulation of training data, … [Read more...]
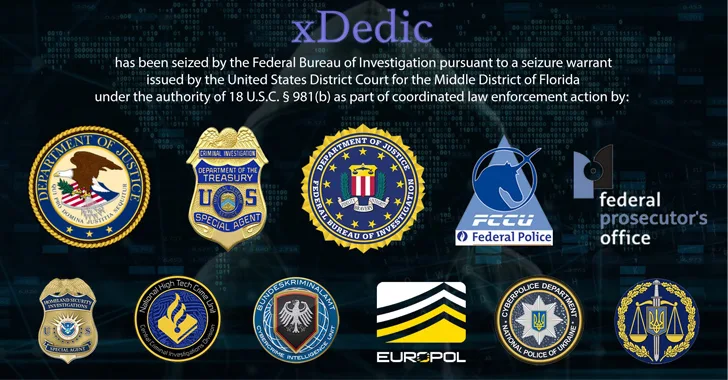
DoJ Charges 19 Worldwide in $68 Million xDedic Dark Web Marketplace Fraud
Jan 08, 2024NewsroomFinancial Fraud / Cybercrime The U.S. Department of Justice (DoJ) said it charged 19 individuals worldwide in connection with the now-defunct xDedic Marketplace, which is estimated to have facilitated more than $68 million in fraud. In wrapping up its investigation into the dark web portal, the agency said the transnational operation was the result of close cooperation with … [Read more...]
North Korea's Cyber Heist: DPRK Hackers Stole $600 Million in Cryptocurrency in 2023
Jan 08, 2024NewsroomCryptocurrency / Financial Crime Threat actors affiliated with the Democratic People's Republic of Korea (also known as North Korea) have plundered at least $600 million in cryptocurrency in 2023. The DPRK "was responsible for almost a third of all funds stolen in crypto attacks last year, despite a 30% reduction from the USD 850 million haul in 2022," blockchain analytics … [Read more...]
Sea Turtle Cyber Espionage Campaign Targets Dutch IT and Telecom Companies
Jan 06, 2024NewsroomCyber Espionage / Supply Chain Attack Telecommunication, media, internet service providers (ISPs), information technology (IT)-service providers, and Kurdish websites in the Netherlands have been targeted as part of a new cyber espionage campaign undertaken by a Türkiye-nexus threat actor known as Sea Turtle. "The infrastructure of the targets was susceptible to supply chain … [Read more...]
Pro-Iranian Hacker Group Targeting Albania with No-Justice Wiper Malware
Jan 06, 2024NewsroomMalware / Cyber Attack The recent wave of cyber attacks targeting Albanian organizations involved the use of a wiper called No-Justice. The findings come from cybersecurity company ClearSky, which said the Windows-based malware "crashes the operating system in a way that it cannot be rebooted." The intrusions have been attributed to an Iranian "psychological operation group" … [Read more...]
- « Previous Page
- 1
- …
- 26
- 27
- 28
- 29
- 30
- …
- 103
- Next Page »