Jan 05, 2024NewsroomEndpoint Security / Malware Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a known malware family that has been attributed to North Korean threat actors. "SpectralBlur is a moderately capable backdoor that can upload/download files, run a shell, update its configuration, delete files, hibernate, or sleep, based on … [Read more...]
Exposed Secrets are Everywhere. Here's How to Tackle Them
Picture this: you stumble upon a concealed secret within your company's source code. Instantly, a wave of panic hits as you grasp the possible consequences. This one hidden secret has the power to pave the way for unauthorized entry, data breaches, and a damaged reputation. Understanding the secret is just the beginning; swift and resolute action becomes imperative. However, lacking the necessary … [Read more...]
Orange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware
Jan 05, 2024NewsroomNetwork Security / Malware Mobile network operator Orange Spain suffered an internet outage for several hours on January 3 after a threat actor used administrator credentials captured by means of stealer malware to hijack the border gateway protocol (BGP) traffic. "The Orange account in the IP network coordination center (RIPE) has suffered improper access that has affected … [Read more...]
Alert: Ivanti Releases Patch for Critical Vulnerability in Endpoint Manager Solution
Jan 05, 2024NewsroomVulnerability / Network Security Ivanti has released security updates to address a critical flaw impacting its Endpoint Manager (EPM) solution that, if successfully exploited, could result in remote code execution (RCE) on susceptible servers. Tracked as CVE-2023-39336, the vulnerability has been rated 9.6 out of 10 on the CVSS scoring system. The shortcoming impacts EPM 2021 … [Read more...]
Russian Hackers Had Covert Access to Ukraine's Telecom Giant for Months
Jan 05, 2024NewsroomCyber Attack / Data Breach Ukrainian cybersecurity authorities have disclosed that the Russian state-sponsored threat actor known as Sandworm was inside telecom operator Kyivstar's systems at least since May 2023. The development was first reported by Reuters. The incident, described as a "powerful hacker attack," first came to light last month, knocking out access to mobile … [Read more...]
New Bandook RAT Variant Resurfaces, Targeting Windows Machines
Jan 05, 2024NewsroomMalware / Cyber Espionage A new variant of remote access trojan called Bandook has been observed being propagated via phishing attacks with an aim to infiltrate Windows machines, underscoring the continuous evolution of the malware. Fortinet FortiGuard Labs, which identified the activity in October 2023, said the malware is distributed via a PDF file that embeds a link to a … [Read more...]
Three Ways To Supercharge Your Software Supply Chain Security
Jan 04, 2024The Hacker NewsEthical Hacking / Vulnerability Assessment Section four of the "Executive Order on Improving the Nation's Cybersecurity" introduced a lot of people in tech to the concept of a "Software Supply Chain" and securing it. If you make software and ever hope to sell it to one or more federal agencies, you have to pay attention to this. Even if you never plan to sell to a … [Read more...]
Beware: 3 Malicious PyPI Packages Found Targeting Linux with Crypto Miners
Jan 04, 2024NewsroomCryptocurrency Miner / Malware Three new malicious packages have been discovered in the Python Package Index (PyPI) open-source repository with capabilities to deploy a cryptocurrency miner on affected Linux devices. The three harmful packages, named modularseven, driftme, and catme, attracted a total of 431 downloads over the past month before they were taken down. "These … [Read more...]
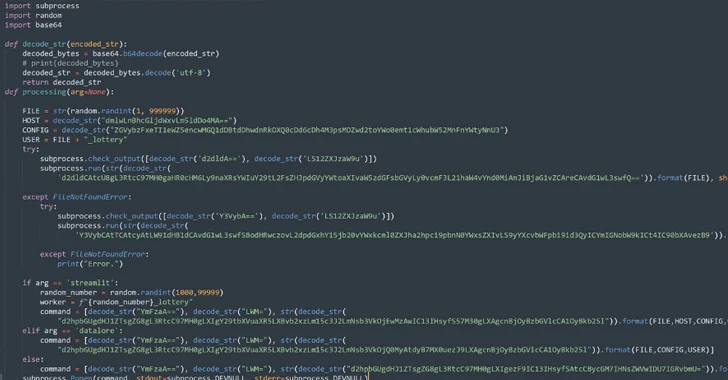
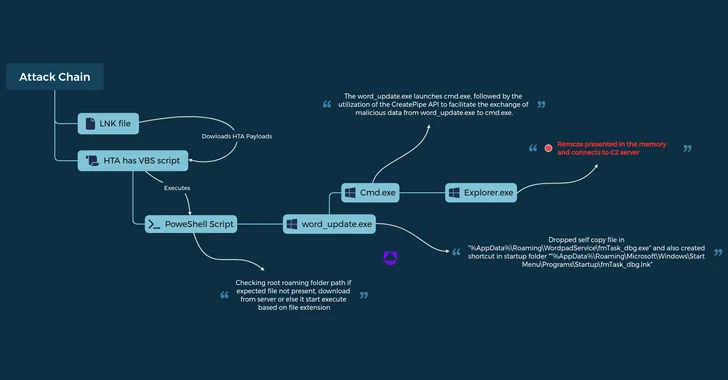
UAC-0050 Group Using New Phishing Tactics to Distribute Remcos RAT
Jan 04, 2024NewsroomSoftware Security / Malware The threat actor known as UAC-0050 is leveraging phishing attacks to distribute Remcos RAT using new strategies to evade detection from security software. "The group's weapon of choice is Remcos RAT, a notorious malware for remote surveillance and control, which has been at the forefront of its espionage arsenal," Uptycs security researchers … [Read more...]
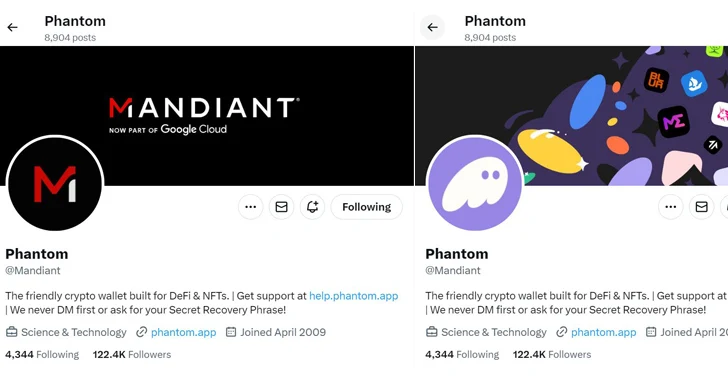
Mandiant's Twitter Account Restored After Six-Hour Crypto Scam Hack
Jan 04, 2024NewsroomCryptocurrency / Social Media American cybersecurity firm and Google Cloud subsidiary Mandiant had its X (formerly Twitter) account compromised for more than six hours by an unknown attacker to propagate a cryptocurrency scam. As of writing, the account has been restored on the social media platform. It's currently not clear how the account was breached. But the hacked … [Read more...]
Malware Using Google MultiLogin Exploit to Maintain Access Despite Password Reset
Jan 03, 2024NewsroomMalware / Data Theft Information stealing malware are actively taking advantage of an undocumented Google OAuth endpoint named MultiLogin to hijack user sessions and allow continuous access to Google services even after a password reset. According to CloudSEK, the critical exploit facilitates session persistence and cookie generation, enabling threat actors to maintain access … [Read more...]
5 Ways to Reduce SaaS Security Risks
As technology adoption has shifted to be employee-led, just in time, and from any location or device, IT and security teams have found themselves contending with an ever-sprawling SaaS attack surface, much of which is often unknown or unmanaged. This greatly increases the risk of identity-based threats, and according to a recent report from CrowdStrike, 80% of breaches today use compromised … [Read more...]
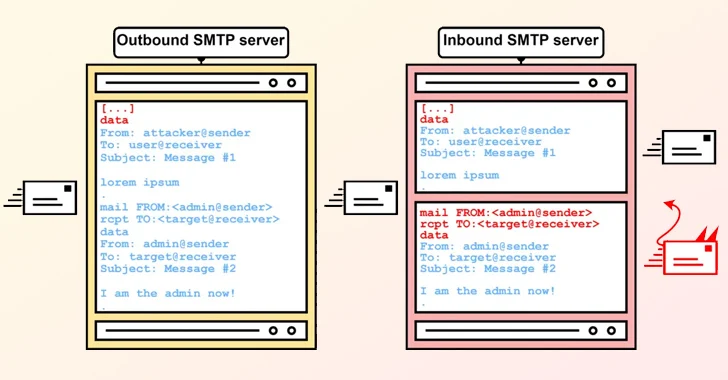
SMTP Smuggling: New Flaw Lets Attackers Bypass Security and Spoof Emails
Jan 03, 2024NewsroomCyber Threat / Email Security A new exploitation technique called Simple Mail Transfer Protocol (SMTP) smuggling can be weaponized by threat actors to send spoofed emails with fake sender addresses while bypassing security measures. "Threat actors could abuse vulnerable SMTP servers worldwide to send malicious emails from arbitrary email addresses, allowing targeted phishing … [Read more...]
DOJ Slams XCast with $10 Million Fine Over Massive Illegal Robocall Operation
Jan 03, 2024NewsroomVoIP Service / Regulatory Compliance The U.S. Department of Justice (DoJ) on Tuesday said it reached a settlement with VoIP service provider XCast over allegations that it facilitated illegal telemarketing campaigns since at least January 2018, in contravention of the Telemarketing Sales Rule (TSR). In addition to prohibiting the company from violating the law, the stipulated … [Read more...]
The Definitive Enterprise Browser Buyer's Guide
Jan 02, 2024The Hacker NewsBrowser Security / Threat Protection Security stakeholders have come to realize that the prominent role the browser has in the modern corporate environment requires a re-evaluation of how it is managed and protected. While not long-ago web-borne risks were still addressed by a patchwork of endpoint, network, and cloud solutions, it is now clear that the partial … [Read more...]
Google Settles $5 Billion Privacy Lawsuit Over Tracking Users in 'Incognito Mode'
Jan 02, 2024NewsroomData Privacy / Online Tracking Google has agreed to settle a lawsuit filed in June 2020 that alleged that the company misled users by tracking their surfing activity who thought that their internet use remained private when using the "incognito" or "private" mode on web browsers. The class-action lawsuit sought at least $5 billion in damages. The settlement terms were not … [Read more...]
New Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections
Jan 01, 2024NewsroomWindows Security / Vulnerability Security researchers have detailed a new variant of a dynamic link library (DLL) search order hijacking technique that could be used by threat actors to bypass security mechanisms and achieve execution of malicious code on systems running Microsoft Windows 10 and Windows 11. The approach "leverages executables commonly found in the trusted … [Read more...]
New Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security
Jan 01, 2024NewsroomEncryption / Network Security Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH) cryptographic network protocol that could allow an attacker to downgrade the connection's security by breaking the integrity of the secure channel. Called Terrapin (CVE-2023-48795, CVSS score: 5.9), the exploit has been described as the … [Read more...]
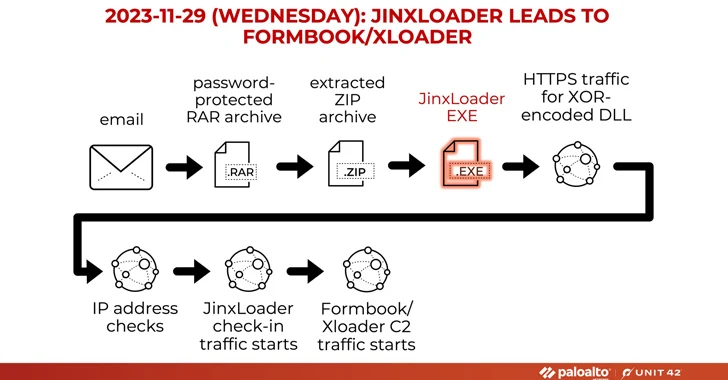
New JinxLoader Targeting Users with Formbook and XLoader Malware
Jan 01, 2024NewsroomMalware / Dark Web A new Go-based malware loader called JinxLoader is being used by threat actors to deliver next-stage payloads such as Formbook and its successor XLoader. The disclosure comes from cybersecurity firms Palo Alto Networks Unit 42 and Symantec, both of which highlighted multi-step attack sequences that led to the deployment of JinxLoader through phishing … [Read more...]
Beware: Scam-as-a-Service Aiding Cybercriminals in Crypto Wallet-Draining Attacks
Dec 30, 2023NewsroomCryptocurrency / Phishing Scam Cybersecurity researchers are warning about an increase in phishing attacks that are capable of draining cryptocurrency wallets. "These threats are unique in their approach, targeting a wide range of blockchain networks, from Ethereum and Binance Smart Chain to Polygon, Avalanche, and almost 20 other networks by using a crypto wallet-draining … [Read more...]
- « Previous Page
- 1
- …
- 27
- 28
- 29
- 30
- 31
- …
- 103
- Next Page »