Jan 18, 2024NewsroomServer Security / Cryptocurrency Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well as the 9Hits Viewer software as part of a multi-pronged monetization strategy. "This is the first documented case of malware deploying the 9Hits application as a payload," cloud security firm Cado said, … [Read more...]
Russian COLDRIVER Hackers Expand Beyond Phishing with Custom Malware
The Russia-linked threat actor known as COLDRIVER has been observed evolving its tradecraft to go beyond credential harvesting to deliver its first-ever custom malware written in the Rust programming language. Google's Threat Analysis Group (TAG), which shared details of the latest activity, said the attack chains leverage PDFs as decoy documents to trigger the infection sequence. The lures are … [Read more...]
TensorFlow CI/CD Flaw Exposed Supply Chain to Poisoning Attacks
Jan 18, 2024NewsroomSupply Chain Attacks / AI Security Continuous integration and continuous delivery (CI/CD) misconfigurations discovered in the open-source TensorFlow machine learning framework could have been exploited to orchestrate supply chain attacks. The misconfigurations could be abused by an attacker to "conduct a supply chain compromise of TensorFlow releases on GitHub and PyPi by … [Read more...]
MFA Spamming and Fatigue: When Security Measures Go Wrong
Jan 18, 2024The Hacker NewsAuthentication Security / Passwords In today's digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical business resources, organizations are increasingly turning to multi-factor authentication (MFA) as a more robust security measure. MFA requires users to provide multiple … [Read more...]
PixieFail UEFI Flaws Expose Millions of Computers to RCE, DoS, and Data Theft
Jan 18, 2024NewsroomFirmware Security / Vulnerability Multiple security vulnerabilities have been disclosed in the TCP/IP network protocol stack of an open-source reference implementation of the Unified Extensible Firmware Interface (UEFI) specification used widely in modern computers. Collectively dubbed PixieFail by Quarkslab, the nine issues reside in the TianoCore EFI Development Kit II (EDK … [Read more...]
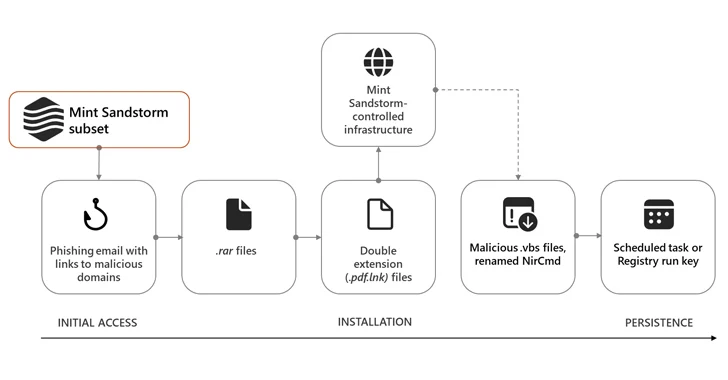
Iranian Hackers Masquerade as Journalists to Spy on Israel-Hamas War Experts
Jan 18, 2024NewsroomCyber Espionage / Threat Intelligence High-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the U.K., and the U.S. have been targeted by an Iranian cyber espionage group called Mind Sandstorm since November 2023. The threat actor "used bespoke phishing lures in an attempt to socially engineer … [Read more...]
PAX PoS Terminal Flaw Could Allow Attackers to Tamper with Transactions
Jan 17, 2024NewsroomFinancial Data / Vulnerability The point-of-sale (PoS) terminals from PAX Technology are impacted by a collection of high-severity vulnerabilities that can be weaponized by threat actors to execute arbitrary code. The STM Cyber R&D team, which reverse engineered the Android-based devices manufactured by the Chinese firm owing to their rapid deployment in Poland, said it … [Read more...]
Combating IP Leaks into AI Applications with Free Discovery and Risk Reduction Automation
Wing Security announced today that it now offers free discovery and a paid tier for automated control over thousands of AI and AI-powered SaaS applications. This will allow companies to better protect their intellectual property (IP) and data against the growing and evolving risks of AI usage. SaaS applications seem to be multiplying by the day, and so does their integration of AI capabilities. … [Read more...]
Feds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials
Jan 17, 2024NewsroomBotnet / Cloud Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) warned that threat actors deploying the AndroxGh0st malware are creating a botnet for "victim identification and exploitation in target networks." A Python-based malware, AndroxGh0st was first documented by Lacework in December 2022, with the … [Read more...]
Webinar: The Art of Privilege Escalation – How Hackers Become Admins
Jan 17, 2024The Hacker NewsCyber Threat / Live Webinar In the digital age, the battleground for security professionals is not only evolving, it's expanding at an alarming rate. The upcoming webinar, "The Art of Privilege Escalation - How Hackers Become Admins," offers an unmissable opportunity for IT security experts to stay ahead in this relentless cyber war. Privilege escalation - the term … [Read more...]
New iShutdown Method Exposes Hidden Spyware Like Pegasus on Your iPhone
Jan 17, 2024NewsroomSpyware / Forensic Analysis Cybersecurity researchers have identified a "lightweight method" called iShutdown for reliably identifying signs of spyware on Apple iOS devices, including notorious threats like NSO Group's Pegasus, QuaDream's Reign, and Intellexa's Predator. Kaspersky, which analyzed a set of iPhones that were compromised with Pegasus, said the infections left … [Read more...]
GitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials
Jan 17, 2024NewsroomVulnerability / Software Security GitHub has revealed that it has rotated some keys in response to a security vulnerability that could be potentially exploited to gain access to credentials within a production container. The Microsoft-owned subsidiary said it was made aware of the problem on December 26, 2023, and that it addressed the issue the same day, in addition to … [Read more...]
Citrix, VMware, and Atlassian Hit with Critical Flaws — Patch ASAP!
Jan 17, 2024NewsroomVulnerability / Cyber Threat Citrix is warning of two zero-day security vulnerabilities in NetScaler ADC (formerly Citrix ADC) and NetScaler Gateway (formerly Citrix Gateway) that are being actively exploited in the wild. The flaws are listed below - CVE-2023-6548 (CVSS score: 5.5) - Authenticated (low privileged) remote code execution on Management Interface (requires … [Read more...]
Zero-Day Alert: Update Chrome Now to Fix New Actively Exploited Vulnerability
Jan 17, 2024NewsroomBrowser Security / Vulnerability Google on Tuesday released updates to fix four security issues in its Chrome browser, including an actively exploited zero-day flaw. The issue, tracked as CVE-2024-0519, concerns an out-of-bounds memory access in the V8 JavaScript and WebAssembly engine, which can be weaponized by threat actors to trigger a crash. "By reading out-of-bounds … [Read more...]
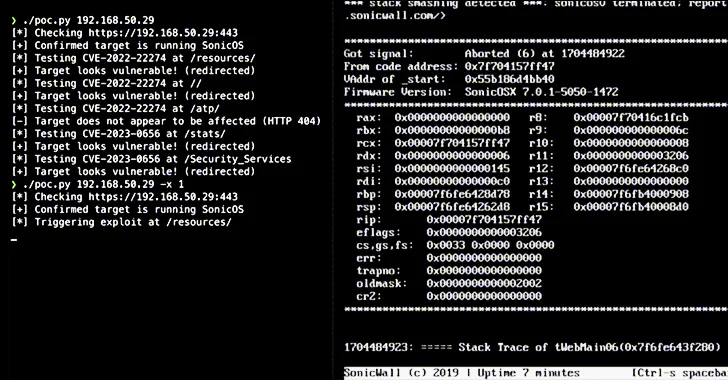
Alert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now
Jan 16, 2024NewsroomVulnerability / Network Security Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be potentially exploited to cause a denial-of-service (DoS) condition and remote code execution (RCE). "The two issues are fundamentally the same but exploitable at different HTTP URI paths due to reuse of a … [Read more...]
Remcos RAT Spreading Through Adult Games in New Attack Wave
Jan 16, 2024NewsroomBotnet / Malware The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games in South Korea. WebHard, short for web hard drive, is a popular online file storage system used to upload, download, and share files in the country. While webhards have been used in the past to deliver njRAT, UDP RAT, and DDoS … [Read more...]
Case Study: The Cookie Privacy Monster in Big Global Retail
Jan 16, 2024The Hacker NewsData Security / Privacy Compliance Explore how an advanced exposure management solution saved a major retail industry client from ending up on the naughty step due to a misconfiguration in its cookie management policy. This wasn't anything malicious, but with modern web environments being so complex, mistakes can happen, and non-compliance fines can be just an … [Read more...]
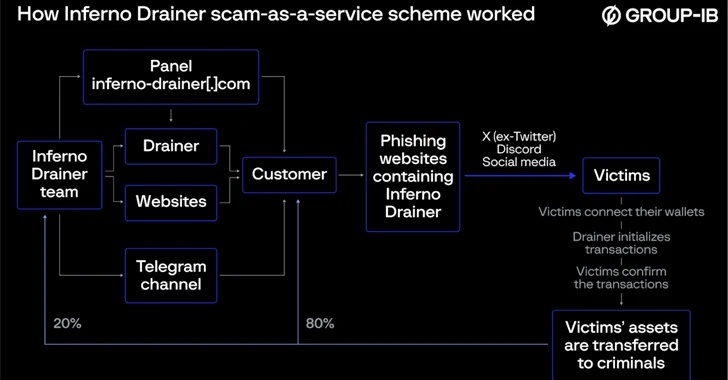
Inferno Malware Masqueraded as Coinbase, Drained $87 Million from 137,000 Victims
Jan 16, 2024NewsroomCryptocurrency / Cyber Threat The operators behind the now-defunct Inferno Drainer created more than 16,000 unique malicious domains over a span of one year between 2022 and 2023. The scheme “leveraged high-quality phishing pages to lure unsuspecting users into connecting their cryptocurrency wallets with the attackers’ infrastructure that spoofed Web3 protocols to trick … [Read more...]
Hackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer
Jan 16, 2024NewsroomCryptocurrency / Windows Security Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy an open-source information stealer called Phemedrone Stealer. "Phemedrone targets web browsers and data from cryptocurrency wallets and messaging apps such as Telegram, Steam, and Discord," Trend Micro researchers Peter Girnus, Aliakbar … [Read more...]
3 Ransomware Group Newcomers to Watch in 2024
The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 4,368 cases. Figure 1: Year over year victims per quarter The rollercoaster ride from explosive growth in 2021 to a momentary dip in 2022 was just a teaser—2023 roared back with the same fervor as 2021, propelling existing groups and ushering in a wave of formidable … [Read more...]
- « Previous Page
- 1
- …
- 24
- 25
- 26
- 27
- 28
- …
- 103
- Next Page »