Threat actors have claimed to have discovered a 0-day vulnerability in Zyxel VPN devices. This revelation was made public through a tweet by the cybersecurity monitoring group MonThreat, which has been closely tracking and reporting on various cyber threats. 🚨 Alleged 0-Day Vulnerability in Zyxel VPNA threat actor has announced the sale of the 0day exploit on a #Zyxel (legacy) VPN … [Read more...]
Muddling Meerkat Using DNS As A Powerful Weapon For Sophistication
Hackers exploit DNS vulnerabilities to redirect users to malicious websites, launch distributed denial-of-service (DDoS) attacks by overwhelming DNS servers, and manipulate domain resolutions to intercept traffic for surveillance or data theft purposes. Infoblox researchers recently revealed “Muddling Meerkat,” a highly sophisticated likely Chinese state actor able to manipulate China’s Great … [Read more...]
Pathfinder – New Attack Steals Sensitive Data From Modern Processors
Microarchitectural side-channel attacks misuse shared processor state to transmit information between security domains. Although they can be used in isolation, they are frequently employed as building blocks for more sophisticated attacks such as Spectre, which uses side channels to achieve controlled speculative execution and data exfiltration. The following cybersecurity … [Read more...]
Beware of New Android Trojan That Executes Malicious Commands on Your Phone
Cybersecurity researchers at XLab have uncovered a new Android malware strain called “Wpeeper.” This sophisticated backdoor Trojan has been designed to infiltrate Android systems and execute a wide range of malicious commands, posing a significant threat to unsuspecting users. Wpeeper’s distribution strategy is particularly cunning. The malware is being distributed through repackaged … [Read more...]
Authorities Seized Platform Used For Paid DDoS
On April 17, 2024, a joint effort between the Dresden Public Prosecutor’s Office and the Cybercrime Competence Center of the Saxony State Criminal Police Office, in collaboration with a U.S. investigative agency, won significantly in the ongoing battle against cybercrime. The operation, aptly named “PowerOFF,” successfully dismantled a criminal online platform in Germany and … [Read more...]
Ex-Infosec Designer Sentenced to Over 21 Years in Prison
Jareh Sebastian Dalke, 32, of Colorado Springs, was sentenced today to 262 months in prison for attempted espionage in connection with his efforts to transmit classified National Defense Information (NDI) to an agent of the Russian Federation. According to the US Department of Justice, Dalke pleaded guilty in 2023 to six counts of attempting to transmit classified NDI to a foreign agent. … [Read more...]
Safari is Not So Private! Safari Flaw Exposing EU iPhone Users to Trackers
A significant security flaw has been identified in Apple’s Safari browser that could potentially expose iPhone users in the European Union to unauthorized tracking. This vulnerability stems from a new feature introduced in iOS 17.4, designed to facilitate the installation of apps from alternative marketplaces directly via Safari. Background of the Flaw The issue was first reported by … [Read more...]
New U.K. Law Bans Default Passwords Like ‘1234’ On Smart Devices
The UK government has introduced a new law to improve the security of smart devices. This law mandates that all smart devices sold in the country must not have weak, default passwords such as ‘1234’. This new law’s primary objective is to protect consumers from cyber threats that exploit basic security vulnerabilities in smart devices such as smartwatches, fitness trackers, home assistants, … [Read more...]
Linux Kernel Vulnerability (CVE-2024-26925) Let Hackers Access Unauthorized Data
In a significant update from the Linux kernel’s security team, a critical vulnerability identified as CVE-2024-26925 has been addressed to bolster the security of systems worldwide. The flaw was found in the netfilter subsystem, specifically within the nf_tables component, which is crucial for packet filtering and classification. Description of the Vulnerability The vulnerability stemmed … [Read more...]
A Costly Mistake: How an Empty S3 Bucket Led to a Massive AWS Bill
AWS Customer Faces Massive Bill Due to Open-Source Tool Misconfiguration. In a startling incident, an AWS customer faced a staggering $1,300 bill for S3 usage, despite creating a single, empty bucket for testing purposes. The culprit? A popular open-source tool with a default configuration that stored backups in the customer’s S3 bucket, leading to a deluge of unauthorized requests. The … [Read more...]
Gemini 1.5 Pro – Powered With Automated Malware Analysis To Detect Zero-Day
Google has introduced Gemini 1.5 Pro for malware analysis, an advanced AI tool capable of processing up to 1 million tokens. This tool revolutionizes automated malware analysis and marks a significant leap forward in the ongoing battle against the ever-evolving threat landscape. Gemini 1.5 Pro for automated malware analysis successfully identified a zero-day threat undetected by any anti-virus … [Read more...]
Rutger Stealer Hijacking Logins from Discord, Skype & other Apps
Cybersecurity experts have identified a new malware, Rutger Stealer, specifically designed to hijack login credentials from users of popular communication platforms such as Discord, Skype, and other applications. This development poses a significant threat to both individual privacy and organizational security. ThreatMon tweeted about the detection of Rutger Stealer, as per their recent … [Read more...]
Token Infrastructure Platform Hacked: $44.5 Million Stolen in Cryptos
Hedgey Finance, a prominent token infrastructure platform, has reported a massive theft of approximately $44.5 million in cryptocurrencies. This incident unfolded rapidly over two hours, affecting operations on Ethereum’s layer-2 network Arbitrum and Binance Smart Chain. Overview of the Attack According to a detailed analysis by blockchain security firm Cyvers, the theft was executed by … [Read more...]
Judge0 Security Flaw Let Attackers Run Arbitrary Code & Gain Root Access
Tanto Security has disclosed critical vulnerabilities in the widely-used open-source service Judge0, which could allow attackers to perform a sandbox escape and gain root access to the host machine. The vulnerabilities, identified as CVE-2024-29021, CVE-2024-28185, and CVE-2024-28189, pose a significant threat to the security of the service, which numerous organizations employ for secure … [Read more...]
HookChain – A New Sophisticated Technique Evades EDR Detection
In the rapidly evolving, complex threat landscape, EDR companies are constantly racing against new vectors. Recently, Helvio Benedito Dias de Carvalho Junior (aka M4v3r1ck) from Sec4US has developed an innovation called “HookChain.” It is an IAT hooking-based technique that utilizes dynamic SSN resolution and indirect system calls. HookChain enables advanced evasion by invisibly … [Read more...]
Hackers Took Just 29-Days From IcedID Infection to Dagon Locker Ransomware
In a sophisticated cyberattack that unfolded over 29 days, cybersecurity analysts have meticulously traced the steps of threat actors from the initial infection with IcedID malware to the eventual deployment of Dagon Locker ransomware. The detailed account of this cyber intrusion provides a chilling example of how quickly and stealthily cybercriminals can compromise an organization’s network … [Read more...]
Telegram Web App Vulnerability Let Attackers Hijack Sessions
A new vulnerability has been discovered in Telegram, allowing a threat actor to hijack a Telegram user session via XSS (Cross-Site Scripting). This vulnerability exists in Telegram WebK versions below 2.0.0. A CVE for this vulnerability is yet to be assigned. However, Telegram has acted swiftly upon this vulnerability and has patched it accordingly. This vulnerability also affects web3 … [Read more...]
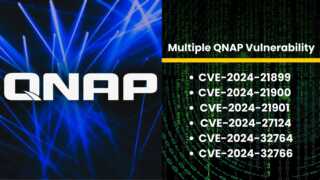
Multiple QNAP Vulnerability Let Hackers Hijack Your NAS
QNAP has disclosed multiple vulnerabilities across its network-attached storage (NAS) systems, which could allow hackers to take control of affected devices. The vulnerabilities impact several versions of QNAP’s operating systems and applications, including QTS, QuTS hero, QuTScloud, and myQNAPcloud. CVE Details CVE-2024-21899: Improper Authentication Vulnerability This critical flaw … [Read more...]
Find Malware With ANY RUN Threat Intelligence YARA Search by File Contents
YARA is a rule-based malware detection tool that utilizes regular expressions and textual/binary signatures to create descriptions (rules) for identifying malicious files. Within ANY.RUN TI, YARA Search allows you to write, edit, test, download, and manage your rules seamlessly, using your existing TI Lookup quota for searches. Find malicious files that match your YARA … [Read more...]
Vulnerability in Apache Project Let Hackers Launch Supply Chain Attacks
Researchers discovered a vulnerability in an archived Apache project, highlighting the risk of using outdated third-party dependencies, where attackers can exploit the way package managers prioritize public repositories to install a malicious package with the same name as a legitimate private dependency. The vulnerability is especially concerning for archived projects, as they likely … [Read more...]
- « Previous Page
- 1
- …
- 5
- 6
- 7
- 8
- 9
- …
- 88
- Next Page »