Source: adtmag.com


Shein to face EU’s strictest rules for online marketplaces
Ultra-fast fashion ecommerce giant Shein will be subject to an additional layer of governance rules targeted at very large online platforms (VLOPs) under the European Union’s Digital Services Act (DSA), the Commission announced Friday. Shein had reported passing an average of 45 million monthly users in the region — which is the threshold for the EU to designate VLOPs under the DSA. The … [Read More...]

Engadget Podcast: Why TikTok will never be the same again
After months of anticipation, President Biden finally signed the TikTok divestment into law this week. It will force ByteDance to either sell TikTok to another company within a year, or see the app banned from US app stores. Is this a wise move to rid control of the social app from the Chinese government, or is it government overreach before TikTok has done anything wrong? Engadget Senior Editor … [Read More...]

These 7 things keep me busy on my high-end gaming PC, and playing games isn't one of them.
Being a PC user since the dawn of the millennium (yeah, I'm old), I always wanted to have a truly high-end gaming PC of my own. My journey from an Intel dual-core to an AMD 8-core gaming PC finally concluded with an RTX 3080 gaming PC in my possession, but once the novelty wore off, I realized I didn't end up spending as much time playing games on it as I imagined I would. Source: … [Read More...]

10 Critical Endpoint Security Tips You Should Know
In today's digital world, where connectivity is rules all, endpoints serve as the gateway to a business's digital kingdom. And because of this, endpoints are one of hackers' favorite targets. According to the IDC, 70% of successful breaches start at the endpoint. Unprotected endpoints provide vulnerable entry points to launch devastating cyberattacks. With IT teams needing to protect more … [Read More...]
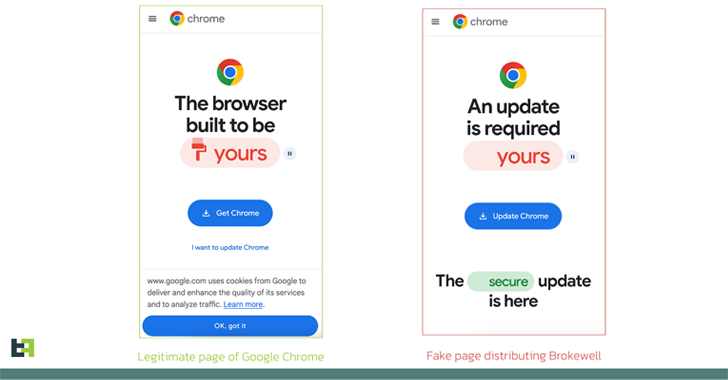
New 'Brokewell' Android Malware Spread Through Fake Browser Updates
Apr 26, 2024NewsroomMobile Security / Cybercrime Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. "Brokewell is a typical modern banking malware equipped with both data-stealing and remote-control capabilities built into the malware," Dutch security firm ThreatFabric said in an analysis published Thursday. The malware is said to be in active … [Read More...]

Palo Alto Networks Outlines Remediation for Critical PAN-OS Flaw Under Attack
Apr 26, 2024NewsroomNetwork Security / Zero Day Palo Alto Networks has shared remediation guidance for a recently disclosed critical security flaw impacting PAN-OS that has come under active exploitation. The vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), could be weaponized to obtain unauthenticated remote shell command execution on susceptible devices. It has been addressed in … [Read More...]
Google Gemini Reportedly Expands to Android 10 to Support Older Smartphones
Google's Gemini app is expanding its compatibility with older Android operating systems, as per a report. Some users have recently highlighted that the Gemini app became available on devices running Android 10. This is a new development as the older versions of the app only supported Android 12 and newer. The users have also said that the app is running without any lag and glitches. Notably, the … [Read More...]

Understanding Hooks in React: The Necessity and Purpose of useState
Introduction: React, a popular JavaScript library for building user interfaces, has evolved significantly over the years. With the introduction of hooks in React 16.8, developers gained a powerful toolset to manage stateful logic and lifecycle events in functional components. In this article, we'll delve into the necessity of hooks, focusing particularly on the useState hook, its purpose, and why … [Read More...]

Building a Neumorphism Loader Using HTML, CSS, and JavaScript
Are you ready to add a touch of elegance to your web projects? In this tutorial, we'll guide you through the process of creating a stunning Neumorphism loader. This project is part of Day 18 of the #100DaysOfCode Challenge. Let's dive in!1. Introduction to Neumorphism: Neumorphism, also known as "soft UI," is a design trend that combines elements of skeuomorphism and flat design to create … [Read More...]

Critical WordPress Automatic Plugin Vulnerability Exploited to Inject Backdoors
Threat actors are exploiting a critical-severity vulnerability in a plugin named WordPress Automatic to inject malicious code into websites, WordPress security scanner WPScan warns. The issue, tracked as CVE-2024-27956 (CVSS score of 9.8), is described as an SQL injection (SQLi) flaw in the plugin’s handling of user authentication in one file, allowing attackers to inject code into a site’s … [Read More...]