Ransomware threats are increasingly targeting data center servers and workloads as the initial step in the attack chain. These systems may not be up-to-date with recommended patches, often run legacy applications without vendor security updates, or may not be scheduled for patch updates to maintain business continuity. As a result, data centers face a high risk of cyber attacks and … [Read more...]
Alert! Oracle Releases Critical Patch Update 2024 – 372 Vulnerabilities are Fixed
Oracle has released its Critical Patch Update (CPU) for April 2024, addressing 372 vulnerabilities across multiple products. The Critical Patch Update provides fixes for security flaws in widely-used Oracle products including Database Server, Fusion Middleware, Enterprise Manager, E-Business Suite, Supply Chain Products Suite, Siebel CRM, Oracle Sun Products, Java SE, and more. The update … [Read more...]
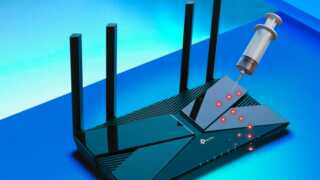
Hackers Exploiting TP-Link Archer Command Injection Vulnerability in the Wild
Cybersecurity researchers have uncovered widespread exploitation of a critical vulnerability in TP-Link Archer routers, which has led to the proliferation of botnet threats. The vulnerability, CVE-2023-1389, allows attackers to execute arbitrary commands on affected devices, potentially granting them access to sensitive information and the ability to hijack the devices for malicious … [Read more...]
Critical PHP Vulnerabilities Let Attackers Inject Commands : Patch Now
Multiple vulnerabilities have been identified in PHP that are associated with Command Injection, Cookie Bypass, Account takeover, and Denial of Service. The CVEs for these vulnerabilities have been given as CVE-2024-1874, CVE-2024-2756, CVE-2024-3096, and CVE-2024-2757. The severity of these vulnerabilities is yet to be categorized. However, the latest version of PHP 8.3.6 has been released, … [Read more...]
NSA, CISA Released Guidance And Best Practices To Secure The AI
In an era where artificial intelligence (AI) systems are becoming increasingly integral to our daily lives, the National Security Agency’s Artificial Intelligence Security Center (NSA AISC) has taken a significant step forward in enhancing cybersecurity. The NSA AISC, in collaboration with several key agencies, including CISA, FBI, ASD ACSC, CCCS, NCSC-NZ, and NCSC-UK, has released a … [Read more...]
Multiple Juniper Networks Flaw Let Attackers Delete Files
The Juniper networks-owned Junos OS has been discovered to have multiple vulnerabilities associated with Denial of Service (DoS), Path Traversal, and Cross-Site Scripting (XSS). The CVEs for these vulnerabilities have been assigned with CVE-2024-30409, CVE-2020-1606, and CVE-2020-1607. The severity for these vulnerabilities ranges between 5.3 (Medium) to 7.5 (High). However, these … [Read more...]
Personal Data Exposed in Massive Global Hack: Understanding the Implications & Guarding Privacy- Axios Security Group
In a digital age where information is the new currency, the recent global hack has once again highlighted the urgent need for enhanced cybersecurity measures. The breach was identified as Midnight Blizzard, from the Russian state-sponsored actor known as NOBELIUM. It has affected Millions of individuals and government agencies worldwide, underscoring the far-reaching consequences of … [Read more...]
Hacker Customize LockBit 3.0 Ransomware To Attack Orgs Worldwide
Hackers leverage the LockBit 3.0 ransomware due to its sophisticated encryption functionalities, which enable them to successfully encrypt victims’ files and request a ransom in order to supply decryption keys. The stealthiness of LockBit 3.0 enhances the attack methods, which allow threat actors to have a better chance of successfully deploying ransomware by enabling them to trespass into … [Read more...]
Popular VPN Software Flaw Let Attackers Crash the Systems
A critical vulnerability has been discovered in a widely used virtual private network (VPN) software, Libreswan, putting millions of users at risk. The flaw, CVE-2024-3652, could allow attackers to remotely crash the affected systems, potentially disrupting critical services and exposing sensitive data. CVE-2024-3652: Vulnerability in Libreswan Versions 3.22 – 4.14 Security researchers … [Read more...]
Iran launched a Major Cyberattack Against Critical Infrastructure in Israel
Cyberattacks have become a critical aspect of international conflicts. The recent cyber attack launched by Iran against Israel’s critical infrastructure is a testament to the evolving nature of geopolitical disputes. This article delves into the technical intricacies of the attack, the response from Israel, the hacker groups involved, and the broader cybersecurity implications. The … [Read more...]
Critical PuTTY Client Vulnerability Lets Attackers Recover Private Keys
A severe vulnerability has been discovered in the PuTTY client and related components, allowing attackers to fully recover NIST P-521 private keys. The PuTTY client generates heavily biased ECDSA nonces when using the NIST P-521 elliptic curve, causing the vulnerability tracked as CVE-2024-31497. PuTTY Client Vulnerability The PuTTY client and all related components, including FileZilla, … [Read more...]
Developer Of Hive RAT Arrested By Authorities for Stealing Login Credentials
A San Fernando Valley man has been taken into custody by federal authorities on criminal charges related to a purported scheme to sell and distribute Hive remote access trojan (RAT). This gave buyers control over the victims’ computers and allowed them to view the victims’ login credentials, private messages, and other personal data. The 24-year-old Van Nuys resident Edmond … [Read more...]
PoC Released For Critical Zero-Click Windows Vulnerability
Microsoft’s wide reach as a target prompted attackers to carry out intensive studies on the vulnerabilities and mitigation tools of their products and protocols. This resulted in a new remote code execution (RCE) WinAPI CreateUri function vulnerability, introduced as part of the CVE-2023-23397 patch. Unlike the previous two-vulnerability RCE chain, this flaw enables zero-click RCE … [Read more...]
StrelaStealer’s Malware Resurgence: What Security Leaders Need to Know in 2024
Stolen credentials are the most common way for hackers to access an organization, according to the 2023 DBIR report. As an analyst for CyOps, Cynet’s team of experts to monitor threat actor activities and protect Cynet clients, I’ve seen how cybercriminals pilfer usernames and passwords, then ruthlessly leverage those lifted logins to wreak havoc on target organizations. The damage can be … [Read more...]
Chinese Chipmaker Nexperia: Gigabytes of Data Stolen
Nexperia, a Chinese chipmaker, has recently been the victim of a massive data breach where gigabytes of sensitive information have been stolen. The incident occurred when the company’s internal security team discovered unauthorized server access. Data Breach Details According to the company’s spokesperson, the breach occurred on March 29, 2024, and the attackers had access to the … [Read more...]
Hackers Launch Business Email Compromise attacks on The Automotive Industry
The automotive industry is experiencing a surge in BEC and VEC attacks, a type of email scam designed to trick employees into transferring money or revealing sensitive information. A recent incident where a fraudster stole $37 million from Toyota Boshoku by tricking an employee into changing bank account information for a wire transfer shows this rise in attacks. Research … [Read more...]
Hackers Actively Using Pupy RAT to Attack Linux Systems
Recent Asian campaigns have seen an uptick in attacks targeting Linux systems, leveraging the notorious Pupy Remote Access Trojan (RAT). This malware, known for its versatility and stealth, has been employed by various threat actors to infiltrate and exploit systems, posing a significant risk to individual and organizational cybersecurity. The Rise of Pupy RAT in Asia Pupy RAT, a … [Read more...]
Earth Hundun’s Hackers Employ Waterbear And Deuterbear Tools For Advanced Cyber Attacks
Hackers always keep evolving their tools to stay ahead of defense systems and exploit new vulnerabilities. Cybersecurity researchers at Trend Micro reported that the Earth Hundun (BlackTech) cyberespionage group has seen a rise in cyberattacks. These attacks exploit the Waterbear virus family, which is renowned for its intricate anti-analysis skills and regularly revised loaders, … [Read more...]
Apache Kafka Flaw Let Attackers Gain Access To Sensitive Data
A new incorrect access control vulnerability has been discovered in Apache Kafka that could allow threat actors to compromise the CIA (Confidentiality, Integrity, and Availability) on the affected resource. This vulnerability has been assigned to CVE-2024-27309, and its severity has yet to be categorized. Apache Kafka is an open-source event streaming platform that offers … [Read more...]
Palo Alto Networks PAN-OS Zero-day Under Active Attack
In a recent security alert, Palo Alto Networks has disclosed a critical vulnerability within its PAN-OS operating system, identified as CVE-2024-3400. This zero-day flaw, found in the GlobalProtect Gateway, is currently under active exploitation by attackers. The vulnerability is classified under CWE-77, indicating an improper neutralization of special elements used in a command (‘Command … [Read more...]
- « Previous Page
- 1
- 2
- 3
- 4
- …
- 78
- Next Page »